Enterprise cloud adoption is growing at a rapid pace. To keep up with the competition, enterprises must evaluate and implement cloud technologies. Many organizations are still unsure how to make the transition to the cloud or what benefits they can expect from doing so. Here we’ll give you an overview of enterprise cloud computing, and discuss some of the benefits companies can reap from making the switch.
Cloud for enterprise is a set of tools and technologies that helps businesses move their data, applications and infrastructure to the cloud. This allows enterprises to take advantage of the many benefits of cloud computing, such as pay-as-you-go pricing, on-demand self-service, rapid elasticity and scalability.
What Is Cloud for Enterprise?
Cloud technology has revolutionized the way businesses operate and exists. It enables enterprises to be more agile, scalable and efficient. Cloud for enterprise is a set of tools and technologies that helps businesses move their data, applications and infrastructure to the cloud. This allows enterprises to take advantage of the many benefits of cloud computing, such as pay-as-you-go pricing, on-demand self-service, rapid elasticity and scalability.
There are many different types of cloud for enterprises, each with its own set of advantages and disadvantages. The three most common types of enterprise clouds are private, public, and hybrid.
Private clouds are owned and operated by a single organization. They offer the greatest degree of control and security but can be expensive to set up and maintain.
Public clouds are owned and operated by a service provider. They are generally less expensive than private clouds but offer less control and security.
Hybrid clouds are a combination of private and public clouds. They offer the best of both worlds but can be more complex to set up and manage.
The decision of which type of cloud for enterprise to use depends on many factors, such as the nature of the business, budget, security requirements, and regulatory compliance.
Enterprise Cloud Security
The term cloud enterprise security refers to the policies, technologies, and controls used to secure data, applications, and infrastructure in a cloud computing environment. It includes both security in the cloud - that is, measures taken by a cloud service provider to protect their own infrastructure and offerings - as well as security provided by the customer (or "enterprise"), often in the form of security as a service.
The shared responsibility model is a key concept in enterprise cloud security. Under this model, the provider and customer both have a role to play in ensuring the security of data and resources in the cloud. The specific responsibilities will vary depending on the type of service being used (IaaS, PaaS or SaaS) and the provider, but typically include tasks such as securing the network, monitoring for threats, managing access control and data encryption.
Network Security
One of the most important aspects of enterprise cloud security is the network. The network is what connects users to the cloud services they use, so it's vital that it is secure. There are a number of different measures that can be taken to secure a network, including firewalls, intrusion detection and prevention systems, and virtual private networks (VPNs).
For enterprises looking for cost-effective solutions, using a free VPN can also provide a significant level of security.
Firewalls act as a barrier between a network and the outside world, blocking traffic that is not authorized to enter. Intrusion detection and prevention systems (IDPS) also monitor network traffic for signs of malicious activity and can take action to block or contain it. Cloud VPNs are another tool that can be used to secure network traffic. They encrypt data as it is sent over the network, making it difficult for unauthorized users to intercept and read it. It's worth noting that using VPNs is legally permitted in most countries, adding a reliable layer of security for network communications.
Cloud Service Security
In addition to securing the network, it is also important to ensure that the cloud services themselves are secure. This includes both the infrastructure that the services run on and the applications that are offered. A number of different measures can be taken to secure cloud services, including access control, data encryption and auditing.
Access control is a measure that can be used to restrict who has access to a cloud service. This can be done using authentication, which requires users to prove their identity before being granted access, or authorization, which controls what level of access each user has. Data encryption is another important security measure. It helps to protect data from being accessed by unauthorized users by encoding it in a way that can only be decoded by those with the correct key.
Data Security
Data is one of the most important assets of any organization, so it's vital that it is properly protected. There are a number of measures that can be taken to secure data, both at rest and in transit.
At rest data security refers to the protection of data that is stored on servers or other devices. This can be done using encryption, which encodes data so that it can only be decoded by authorized users. In transit data security refers to the protection of data as it is being sent from one location to another. This can be done using secure protocols such as SSL/TLS.
Endpoint Security
Another important aspect of enterprise cloud security is endpoint security. Endpoints are the devices that users connect to the network to access cloud services. They can be laptops, smartphones, tablets or any other type of device. It's important to ensure that endpoints are secure, as they can provide a way for unauthorized users to gain access to data and resources.
It's important to choose a solution that is compatible with the specific cloud services that an organization is using. It's also important to ensure that the solution can scale as the organization grows.
Read more about Enterprise Cloud
- Private Cloud vs On-Premise
- Top Cloud Providers in 2022
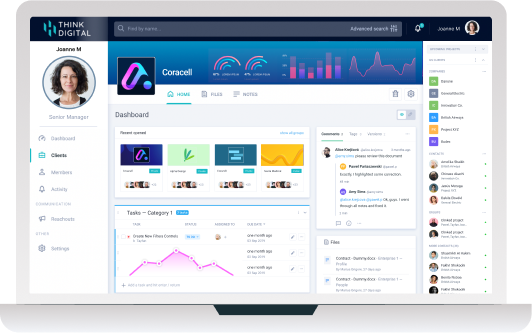
- Cloud Collaboration: Benefits and Tools
- Private Cloud vs Public Cloud: Crucial Differences
- Enterprise Cloud Storage: Make The Right Choice
- Data Storage Companies: The Best Of 2022







Let Us Know What You Thought about this Post.
Put your Comment Below.