In the increasingly digital world we live in, and with more 'traditional' law firms adopting cloud-based digital platforms, legal businesses, more than any other professional services business, are increasingly being targeted by cyber criminals. The large amounts of highly confidential client data that is customary for legal firms to manage, makes for an appealing target for these bad actors.
Indeed, according to a recent report, individual ransomware payouts exceed, on average, over $1 million, and in same cases, can even present an existential threat to firms. Professional industry sector, including the legal services, is one of the top 5 most targeted by cyber espionage along with financial, government, information and healthcare sectors.
In 2020, there were a total of 1,001 data breaches and over 155,000,000 records exposed in the US.
 Source: Statista
Source: Statista
Security and compliance have never been more crucial. But what can we do to thwart the scourge of cyber criminals seemingly bent on breaching security systems for nefarious purposes? And how do we create a culture for our internal teams that embraces the processes that deliver compliance and ensure security for our valuable data?
It starts with your team
Your employees are your first line of defense against compliance failures. Whether you use group training or one-on-one sessions, it’s important that each and every employee knows the ripple effect that a single compliance failure could have. For example, a security breach that goes undetected for even a day could result in the theft of customer data and subsequently, loss of business.
A compliance failure can also have a profound impact on your company’s reputation. In fact, a recent study showed that 60 percent of clients would stop doing business with a company after a data breach - Trust, for the providers of legal services, is quite obviously of critical importance. Clearly, it’s essential to make sure your employees understand the importance of compliance and how their actions can impact the company as a whole.
But before we get into the discussion around security and compliance, let's be clear about the distinction between both, as often, even seasoned professionals in the field interchange terminologies.
Security and compliance - the distinction
Many professionals use the terms 'security' and 'compliance' interchangeably, but there is a big difference between the two. Let's first distinguish the differences and establish the objectives of each.
What is information security?
Information security is the practice of protecting electronic or digitally stored information by mitigating information risks and vulnerabilities. It is concerned with protecting your IT systems and securing data from cyberattacks and other threats.
Crucially, security is practiced for its own sake, and not to satisfy a third party's needs - it's never truly finished. With new threats and continuously evolving practices by cyber criminals, it's essential that professional organisations perpetually maintain and further improve their security systems and processes.
While security is an ongoing process that must be continually refined and updated, compliance is typically about checking off a list of requirements, that once complete, requires no additional input.
What is compliance?
Compliance is the adherence to a set of rules or regulations and is practiced in order to satisfy external requirements and facilitate business operations.
Compliance is typically driven by business needs rather than technical needs. For example, a company may need to ensure it is compliant with government regulations or meet customer requirements. Compliance can be a challenge.
While compliance is 'completed' once all of the boxes have been ticked, it shouldn't be considered as a 'set it and forget it' process. As with every aspect of our businesses, continual development ensures systems remain robust and our approach accordant. It is an ongoing process that should be monitored and evaluated regularly to ensure that it remains effective.
Compliance is a process that is often misunderstood. Too often, people view compliance as a series of hoops to jump through in order to avoid punishment. While in some cases this might feel like an entirely reasonable assessment, the objective of compliance is not to wrap teams in red tape and bureaucracy. In fact, the most important part of compliance is not the avoidance of punishment, but the creation of a system in which everyone can succeed.
Together, information security and compliance help protect an organization's confidential data from unauthorized access or use and provide processes that increase the chances for success in achieving this crucial goal.
Bringing security and compliance together
Security compliance management (SCM) is the process of ensuring that an organization's security infrastructure complies with applicable regulatory and professional requirements and internal policies. SCM encompasses a variety of activities, including risk assessment, policy development and enforcement, security awareness training, and periodic reviews of security controls.
An effective SCM program can help organizations protect their data and systems from unauthorized access, theft, or destruction.
Formalising a thorough compliance management system ensures that your firm is supporting your internal teams in attaining compliance best practice in order to achieve robust security. Furthermore, the SCM ensures that your data is always secure and that your business is in compliance with all relevant regulations.
A security and compliance management system can help you improve your organization's overall security posture. Implementing an SCM program not only supports the credibility of your firm, it also protects your reputation and can significantly protect against costly litigation should a data breach attempt be made.
Unfortunately, when it comes to the security of their data, many legal businesses view compliance management as an afterthought. This has the potential to be a costly mistake, considering the implications outlined previously.
How a client portal can support security and compliance
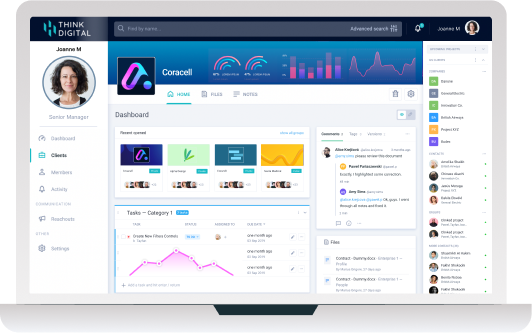
A client portal is a web-based application that provides a secure, central location for legal firms and their clients to access and manage their case information and interact with one another.
For legal firms looking to enhance their security and compliance while providing a cloud-based platform that supports ease of use and collaboration, here are just some of the features your client portal will feature.
It should be noted that, as mentioned earlier, your team should be at the front end of the adoption of any new system or workflow. While the following list of functionality my seem daunting to the uninitiated, some custom client portals, such as Clinked.com, are incredibly intuitive and require little in the way of onboarding or training. This is key to the successful adoption and implementation of your client portal-enabled security and compliance efforts.
Secure access
When considering a client portal you should demand, at the very least, 256 bit, bank-grade security. This is the standard level of security for client portals - you shouldn't accept anything less. Combined with two-factor authentication and controlled logins, security is by far, the most important aspect of your client portal.
Complex passwords
You need to ensure that your team aren't using one of the myriad of passwords that can be cracked in less than a second... (a worrying example: 123456 is used by over 100 million users worldwide and can be cracked in under a second).
An optional 'complex password' setup, when selected by the administrator, requires your users to use a combination of letters, numbers and special characters for their password, exponentially increasing the security of your data.
User based permissions
The administrator of the platform is able to allocate each user with set permissions, enabling appropriate viewing or editor rights. Providing users with specific permissions is one of the most important aspects of managing your client portal. This is especially true when multiple users are able to access client data.
By allowing each user of the platform with specific permissions, you can ensure that they are able to only access the areas of the site and of different clients' information that they have approval for.
Audit trail
Knowing who has created, viewed, accessed, downloaded, deleted or otherwise interacted with digital assets, when and from which device, allows for unsurpassed tracking of user activity. As well as previewing within the platform, administrators are able to generate csv format audit trails.
Additional client portal functionality
In addition to the functionality detailed above, listed her are some more features you should demand from a secure client portal:
- White label customisation
- Virtual data room (VDR)
- Group chat
- File sharing
- Legally binding e-signature functionality
- Document version control
- Integrations
Transparency, enabled by compliance and security
It's important to note at this point, that while there are a raft of functions within Clinked that enhance compliance and protect data, these very same tools allow for greater transparency amongst internal teams and external clients. It would wrong to build a fortress around data that precludes efficient working and collaboration. the sharing of ideas, selective transparency and managed access are at the heart of Clinked's offering.
In conclusion
The compliance and security of your data is critical to your business and enabling your internal teams to be securely compliant is critical for efficiency.
Compliance is important to ensure you’re operating within the law, providing consistency of service to your clients and reducing your risk. Lack of security can lead to data breaches, which can be costly, may result in litigation and have the potential to be damaging to your business. The good news is that Clinked provides a secure platform that is compliant with industry regulations, so you can be confident in securely managing yours and your clients' data.
To find out more about how Clinked can support your security and compliance management sign up for the April 6th webinar today.
About Clinked
Clinked.com is the software as a service (SaaS) company that provides an online document, digital asset management and collaboration tool for organisations of all sizes.
Clinked client portal software was created with the goal of helping predominantly professional services firms with streamlining their compliance efforts with efficiency and crucially, security at the heart of their offering.
Since its inception, the company has seen a surge in interest from legal firms of all sizes looking for a better way to manage their assets, boost client engagement and simplify asset audit tracking.
In fact, Clinked is incredibly versatile in that law firms are able to build bespoke functionality on top of the core product.
For conscientious legal firms, one of the biggest benefits of using Clinked is the ability to create custom workflows that can be tailored to meet the specific needs of their business and simplify the collection, collation and access to client documentation, securely.
To find out more about how Clinked can support your business, contact Clinked.






Let Us Know What You Thought about this Post.
Put your Comment Below.