Cryptocurrency security is essential to protect your assets against malicious activity. Your private key can be vulnerable to hacking. Clinked can provide multi-level authentication that is needed for cryptocurrency security while keeping everything streamlined and user-friendly.
Cryptocurrency has taken the world and stock markets by storm since it was created in 2009. It is a weekly hot topic for news outlets and financial brokers worldwide. As of 2022, 4% of the world’s population owns a form of cryptocurrency. While not many countries actually call it a valid currency, except for El Salvador, many more countries and businesses accept it as payment for goods and services.
While cryptocurrency can be a complex concept to grasp for the average person, it has many favorable aspects and will only continue to grow in popularity. One main feature that has caused many people to be interested in cryptocurrency is its lack of control and influence from any major financial institution or government. With the Gen Z generation rejecting traditional banking for more control of their finances and to combat hyperinflation, cryptocurrency fits into their plans perfectly.
What is Cryptocurrency?
Creating cryptocurrency is not easy and can be pretty complicated to understand at a basic level. Still, essentially it is a digital currency used as a method of payment using a range of encryption algorithms. The process of creating a new cryptocurrency is called “mining,” where supercomputers generate numbers that solve the “Blockchain” encryptions or puzzles, where the currency is kept. If the computers manage to break the puzzles, crypto tokens are created. Since cryptocurrency is so popular, blockchain encryptions or puzzles are a lot more energy intensive and complicated, as the more people that mine, the more complex the puzzles become.
In today’s world, as cryptocurrencies increase in value and popularity, cybercrime and security threats are developing rapidly. It is a significant concern to many businesses in the US as over 2000 American companies will now accept cryptocurrency as a valid payment method. Having a cyber security program or a delegated Chief of Information Security is a must for any business that operates on the internet or with cryptocurrency.
Cybercriminal Activity for Cryptocurrencies
Along with so many forms of technology, everything is changing rapidly, and it is hard to keep up. Anyone who has invested in Cryptocurrency should think about Cryptocurrency security. The most common ways cryptocurrency has been hacked are through key theft, software vulnerabilities, and fake Crypto scams.
Key theft involves gaining contact with a private set of passwords (the key) that gives access to a cryptocurrency account; without these passwords, it is impossible to infiltrate. The keys can be stored in either hot (within the software) or cold wallets (away from personal devices in physical hardware).
Along with key theft, exploiting vulnerabilities in a company’s security system or software can cause a crypto hack, for example, changing the administrative privileges for the blockchain, which allows complete access and, ultimately, theft.
Cybercriminals will also use the most original hack of all, the scam. Offering fake investment opportunities, financial proposals, and even fake love matches can gain access to someone’s personal device, leaving them susceptible.
As stated above, the complexity of cryptocurrency, its origin, and how they are created is hard to comprehend. Due to the popularity of cryptocurrency, many consumers who have bought the currency do not entirely understand the process. Ever heard the saying “knowledge is power”? For cybercriminals, a lack of knowledge is power for them, with a range of exposed personal devices and software to choose from.
To stop any theft of cryptocurrencies, cryptocurrency security is necessary. The safe storage of your private key is essential to protect your assets against malicious activity. As many people keep this information on their personal devices and not within a cyber security program, the key can be vulnerable to hacking and the loss of all their money.
Be diligent not just about whom you continue to do business with but with the cryptocurrency security surrounding your assets. Keep up to date with the various new trends in crypto hacking to ensure your system can withstand it.
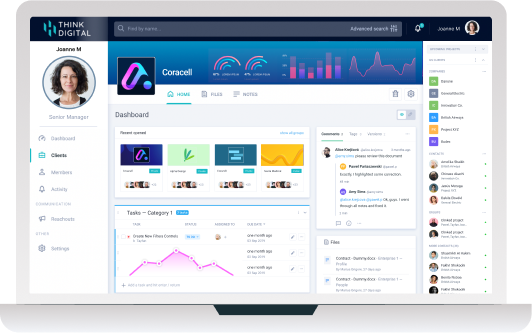
Also, use multi-level authentication on all your possessions, including your security key, as it provides an extra layer of protection. The blockchain and key already give a layer of protection, but in this age of technology, you can never be too careful. A Clinked portal can give that multi-level authentication that is needed, client portals in general can help with cryptocurrency security while keeping everything streamlined and user-friendly.
Legal Implications of Cryptocurrency Losses
Even though cryptocurrency has been bought by over 300 million people worldwide, it is not recognized as a legal currency, with the exception of one country. So what are the legal implications of the theft of something that is not legally recognized?
Even though cryptocurrency has a decentralized nature and no governing body controls it, there are still quite a few legal implications for cybercriminals. Cryptocurrency security is a high priority for the Biden administration. In March 2022, cybersecurity laws were ordered to be prioritized by the American government to combat any malicious activity on any digital assets.
The Federal Trade Commission is monitoring the trends in cyber criminality around cryptocurrencies to clamp down on suspicious activity and theft.
Along with regulatory actions from different government bodies, law enforcement has been focused on clamping down on digital thefts, with large amounts of stolen cryptocurrencies recovered. This increased scrutiny also highlights the importance of understanding crypto taxes.
With law enforcement and governments recognizing that consumers and businesses are using cryptocurrencies, organizations trading in cryptocurrencies should be proactive in their own cryptocurrency security. Any business trading with cryptocurrencies is expected to adhere to the same cybersecurity laws as traditional banking.
Business owners should construct any policies and procedures for cyber data, information, and assets safety and security. Clinked can help in sharing these new policies with employees and clients securely. Also, various response protocols should be in place for when a cryptocurrency security attack occurs. These procedures can help in the recovery of their assets if an attack should occur.
Any cyber hacking that results in the loss of assets can be exposed to litigation. Some litigants have stated that negligent behavior has arisen from crypto exchanges, where consumers can buy cryptocurrencies that have already gone through the mining process, and traditional companies. They have been remiss in not preventing cyber criminals from entering their software and keeping up to date with their cryptocurrency security defenses and protocols.
Conclusion
Investing in cryptocurrency is a new way of making and investing money, taking the financial world and Wall Street by storm. It is a section of commerce and financials that will only continue to grow and prosper. Due to its successful debut and continued accomplishments, it will be inundated with people willing to dupe people out of their assets.
By using a service portal like Clinked, your information can be kept safe. It is an easier and more secure way to ensure diligence from consumers, staff, and customers. By having a more secure way to save and use your information, cybercriminals can be slowed down and hopefully caught. To learn more about emerging high tech theft, you may want to read our recent article Do AI-Influenced Cyber-Attacks Pose a Big Problem for Law Firms?
Related articles:
- 3 Ways to Modernize Data Protection, Governance, and Compliance
- Do AI-Influenced Cyber-Attacks Pose a Big Problem for Law Firms?
- Security and compliance for legal firms - why it matters and how it's achieved
- Law Practice Management Software
- What Are the Biggest Challenges Facing the Legal Profession in 2022?
- Why A Client Portal Is Ideal For Law Firms
- What Is Your Lawyer Personality Type?







Let Us Know What You Thought about this Post.
Put your Comment Below.